Data Center Security Automation: Why Robot Dogs Signal an M&A Opportunity Buyers Are Missing
Data center security automation is getting a makeover — and the media is missing the real story. Headlines about quadruped robot dogs patrolling data center floors treat the development as a novelty. A Boston Dynamics Spot wearing a Christmas sweater. A Ghost Robotics Vision 60 doing the rounds at an Air Force base. Compelling visuals, thin analysis. The structural implication — a $600 billion infrastructure buildout creating a physical security crisis that no existing SaaS vendor is positioned to solve — is hiding in plain sight.
For SaaS founders building in the physical security or data center management space, for PE and VC investors evaluating security software targets, and for enterprise CTOs navigating vendor selection at hyperscale facilities: this is the analysis the robot dog news cycle hasn’t produced yet.
The Scale Problem No Software Vendor Has Solved
The numbers are staggering. The five largest hyperscalers — Amazon, Microsoft, Alphabet, Meta, and Oracle — have collectively committed to spending between $660 and $690 billion in capital expenditure in 2026. Roughly 75 percent of that total is directed at AI infrastructure. As of late 2025, Synergy Research Group counted 1,297 operational hyperscale data centers worldwide — nearly triple the number from early 2018 — with a pipeline of 770 additional facilities at various stages of construction.
Each of those facilities needs to be physically secured, monitored, and inspected. That is not a software problem. It is a physical operational problem at a scale the industry has never encountered. The gap between growing data center footprints and the available human workforce to manage them is real. Gartner predicted half of cloud data centers would leverage advanced robots by 2025, and the deployment evidence is arriving in waves.
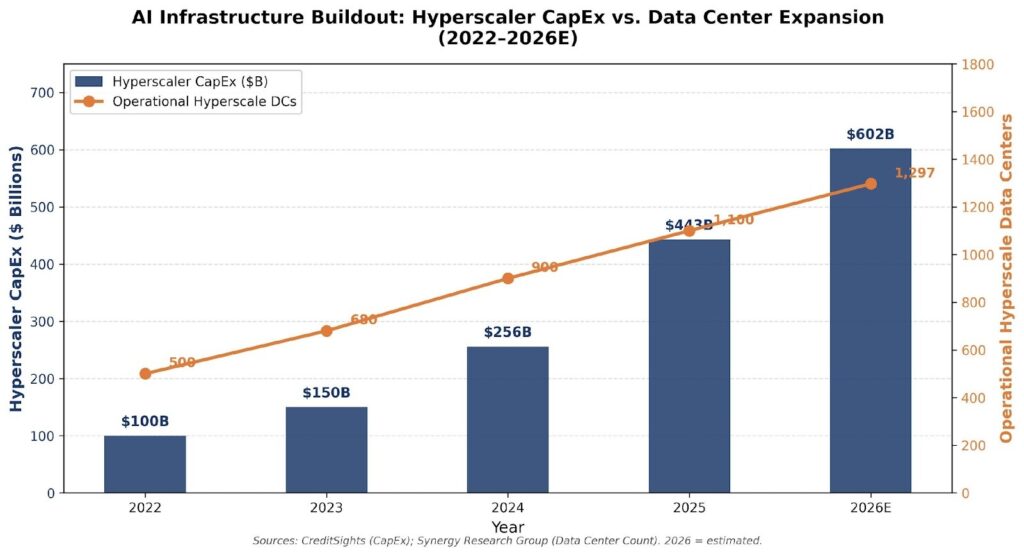
Figure 1: AI Infrastructure Buildout — Hyperscaler CapEx ($B) vs. Operational Data Center Count (2022–2026E). Sources: CreditSights; Synergy Research Group.
| Key Insight for M&A PractitionersThe physical footprint of AI infrastructure is expanding at a rate that overwhelms traditional security staffing models. This is not a trend. It is a structural gap — and structural gaps create M&A markets. |
What Boston Dynamics and Ghost Robotics Actually Represent
Before we get to the M&A opportunity, let’s be precise about what the hardware players represent — and what they don’t.
Boston Dynamics‘s Spot robot starts at $74,500 and is purpose-built for industrial inspection. Equipped with LiDAR, thermal cameras, and an SDK for custom development, it’s a mobile automation platform, not a finished security product. Novva Data Centers, an early adopter, describes their experience plainly: the out-of-the-box Spot lacked integration with their existing systems. They needed to add custom software for facial recognition, meter reading, autonomous route navigation, and integration with their broader DCIM stack. That integration work was contracted to Rightpoint, a Genpact company. The robot provided the legs. The software — and the third party to build it — provided the value.
Ghost Robotics plays a different game. Their Vision 60 Q-UGV, estimated at $150,000+ depending on configuration, is built for defense and security operations. The US Air Force, Space Force, and Coast Guard have all deployed Ghost Robotics platforms for perimeter security and anomaly detection. Ghost Robotics’ CEO Jiren Parikh describes their business model as putting “edge processing on the dog and in the doghouse” — the robot is a hardware delivery vehicle for a software and AI analytics stack. Ghost Robotics is closer to a data company than a robotics company. In February 2026, Ghost Robotics unveiled a new manipulator arm for their Vision 60 platform, signaling continued hardware expansion.
Neither company is the acquisition target that enterprise software buyers should be hunting. Both are capital-intensive hardware businesses with modest software margins. The real opportunity lies in the layer above them.
The Data Center Security Software Layer Acquirers Keep Missing
Here is the structural insight that the robot dog narrative consistently obscures: the quadruped robot is an endpoint, not a system. The value in physical security automation is created by the software that ingests sensor data, applies AI-driven anomaly detection, integrates with DCIM platforms, triggers SOC escalation workflows, and maintains audit trails for compliance.
This is exactly the framework we apply in our M&A due diligence analysis of enterprise technology infrastructure. When evaluating a data center operator or security technology vendor, the question is never “do you have the hardware?” It is “do you own the workflow?”
The current market has four distinct software categories operating in this space:
1. Traditional Physical Security SaaS (Camera / Access Control)
Vendors like Verkada, Openpath, and Brivo provide camera management, access control, and basic analytics. These are horizontally-designed platforms built for office buildings, not 1.5-million-square-foot AI campuses with GPU cooling systems, high-voltage substations, and biometric security requirements. Their switching costs are moderate; their workflow ownership is shallow. Acquisition premium: low.
2. Security Operations Center (SOC) SaaS
Platforms like Pagerduty, Splunk, and Sumo Logic ingest security event data and manage incident response workflows. They are excellent at the software layer but have zero physical awareness. A temperature anomaly in Server Row 47 at 3 AM does not generate a Splunk alert unless someone has built the integration between the physical sensor network and the SOC platform. That integration gap is currently being filled by systems integrators — not by the SOC vendors themselves. Acquisition premium: moderate, but only for vendors actively building physical integration.
3. DCIM Software (Data Center Infrastructure Management)
Vertiv, Nlyte, and Sunbird provide the management layer for data center assets — power, cooling, capacity, and physical infrastructure. DCIM is structurally positioned to absorb the robot integration layer, but most vendors have not moved aggressively in that direction. The opportunity is visible; the execution is absent. Acquisition premium: high for DCIM vendors actively integrating autonomous inspection workflows.
4. AI Video Analytics and Anomaly Detection SaaS
This is the fastest-growing and most undervalued category in the data center security automation stack. Vendors building AI models specifically for data center environments — thermal drift detection, equipment anomaly identification, access pattern analysis — occupy the highest-value position. They don’t need to own the robot. They need to be the intelligence layer that every robot, camera, and sensor feeds. Workflow ownership here is deep, switching costs are high, and the data moat compounds over time. Acquisition premium: highest in the category.
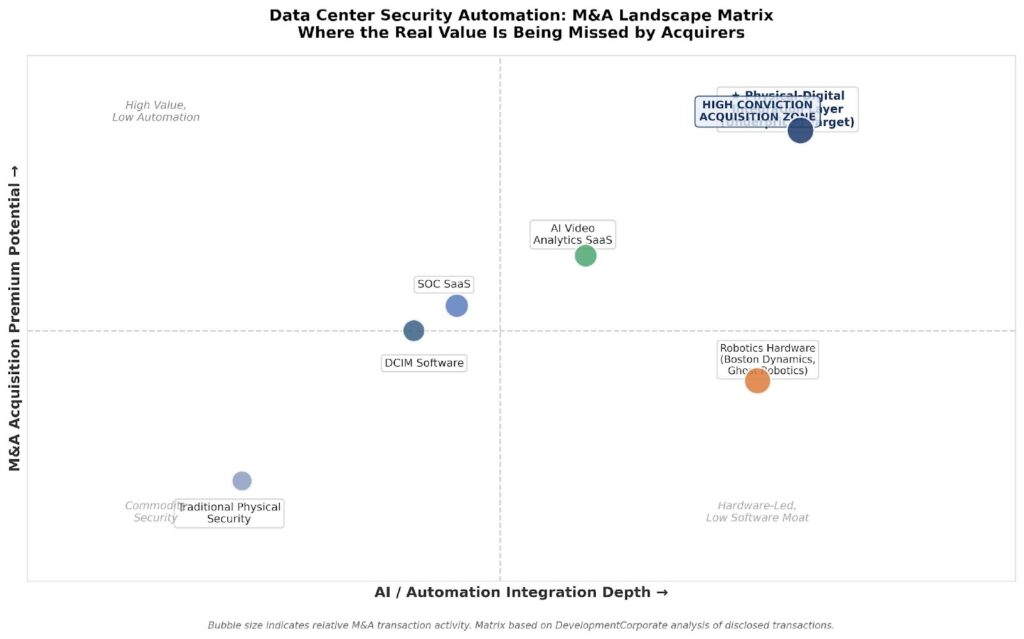
Figure 2: Data Center Security Automation M&A Landscape Matrix. The Physical-Digital Integration Layer represents the highest-conviction acquisition target. Source: DevelopmentCorporate analysis.
Due Diligence Red Flags in Data Center Security Automation Targets
As we noted in our analysis of what VC rejection signals mean for M&A buyers, when a category attracts media attention without corresponding M&A sophistication, the valuation gap is usually exploitable in the near term — but only for buyers who apply disciplined diligence. Three specific red flags apply here:
Red Flag #1: The “We Have a Robot” Narrative. Any physical security vendor claiming competitive differentiation primarily because they have a deployment partnership with Boston Dynamics or a license agreement for Ghost Robotics integration should be treated with skepticism. The robot is hardware. The moat is software. Ask: if Boston Dynamics ships its next-generation Spot to every competitor tomorrow, does your competitive position change? If the answer is yes, the moat isn’t there.
Red Flag #2: Shallow DCIM Integration. A security automation platform that operates as a standalone island — not integrated with the data center’s power, cooling, and capacity management systems — is a feature, not a platform. The acquisition premium belongs to the vendor whose security events feed directly into the operational decision-making loop of the facility. Ask for API integration depth and number of DCIM connectors.
Red Flag #3: Single-Vendor Dependency. We have seen this pattern repeatedly in our analysis of the user research SaaS bifurcation. Execution tools that depend on a single upstream vendor (whether a hardware robot or a cloud platform) carry concentration risk that shows up in ARR retention analysis. Data center security automation vendors that support only one robot platform are priced the same as multi-platform infrastructure vendors — and shouldn’t be.
| Diligence Framework: The Three Questions1. Does this platform own a workflow, or does it monitor one?2. What happens to competitive position if the hardware platform is commoditized?3. How many DCIM and SOC integrations are live — not just announced? |
What This Means for Each Audience
For SaaS Founders
If you are building in physical security, DCIM, or AI analytics for industrial environments, the hyperscaler buildout is the most significant demand signal in your market’s history. The acquisition window is open. The current SaaS exit environment rewards founders who can demonstrate workflow ownership — not those who sell features. If your platform integrates with the physical robotics layer AND feeds into the SOC/DCIM stack, you are building the kind of infrastructure-grade switching cost that commands a premium multiple. Start building those integration stories now, before the first wave of consolidation closes.
For PE and VC Investors
The data center security automation category is currently priced as a collection of point solutions. The market hasn’t yet recognized that what’s being built — the integration layer between physical autonomous systems and digital security operations — is functionally equivalent to mission-critical enterprise software. Vendors commanding strong NRR (above 115%) with live DCIM and SOC integrations are being evaluated at execution-tool multiples. Applying the bifurcation framework we use in enterprise SaaS M&A analysis — separating workflow-owning platforms from automation execution tools — will surface targets that are materially undervalued in the current market.
For Enterprise CTOs and CPOs
Your vendor selection decision in this category is also a strategic risk management decision. As we documented in our analysis of AI ROI data across 6,000 CEOs and CFOs, the gap between AI adoption and measurable impact is wide. Physical security automation is no different. Before deploying robotics-based security systems, demand integration evidence — not demo videos. Ask vendors to demonstrate live API connectivity to your DCIM platform. Require SLAs for anomaly detection precision and recall rates. Treat any vendor whose differentiation rests primarily on the robot brand (Boston Dynamics, Ghost Robotics) rather than the software stack as a hardware reseller, not an enterprise software partner.
Why the Acquisition Window Is Open Now — and Won’t Stay Open Long
Consolidation in enterprise security software follows a predictable pattern. A demand shock (in this case, $600B+ in AI infrastructure capex) creates a fragmented landscape of point solutions. PE-backed strategics and hyperscale operators begin identifying integration requirements. The first wave of acquisitions is made at below-platform multiples because buyers are still applying feature-tool frameworks to infrastructure-grade assets. Then the narrative shifts, multiples compress upward, and the window closes.
We are currently in the early phase of that pattern for data center security automation. The market is populated by vendors that built for today’s data center footprint — not for the 770-facility pipeline that Synergy Research has identified. The acquirer who acts before the narrative catches up will pay infrastructure multiples for infrastructure assets. The acquirer who waits for the market consensus will pay platform multiples for the same assets. That gap is the alpha in this category.
Conclusion: Stop Looking at the Robot, Start Auditing the Software Stack
The robot dog at the data center is a symptom of a much larger structural shift. The AI infrastructure buildout — $602 billion in hyperscaler capex in 2026 alone, 1,297 operational hyperscale data centers and growing — has created a physical security and inspection problem that exceeds the capacity of human labor models. Quadruped robots are the most visible response. But the real M&A story is in the software layer that makes those robots useful.
Data center security automation is not a robotics story. It is a workflow ownership story. The vendors that own the integration between physical autonomous systems, DCIM platforms, and SOC workflows are building the kind of organizational infrastructure that commands durable acquisition premiums. Right now, most of them are being priced as point solutions.
The contrarian position: the robot dog news cycle is generating noise that obscures signal. The signal is that a new infrastructure software category is being born inside the AI capex buildout — and most acquirers haven’t started looking.
| Ready to Apply This Framework to Your Portfolio or Pipeline?DevelopmentCorporate LLC provides M&A advisory services to enterprise SaaS founders, PE investors, and corporate development teams. If you are evaluating targets in physical security automation, DCIM, or AI infrastructure software, contact us for a confidential assessment. Visit developmentcorporate.com or schedule a 15-minute introductory call via our Competitive Analysis service page. |