The Vercel Breach: Why “Front-End Infrastructure” Is the New Soft Underbelly of SaaS M&A
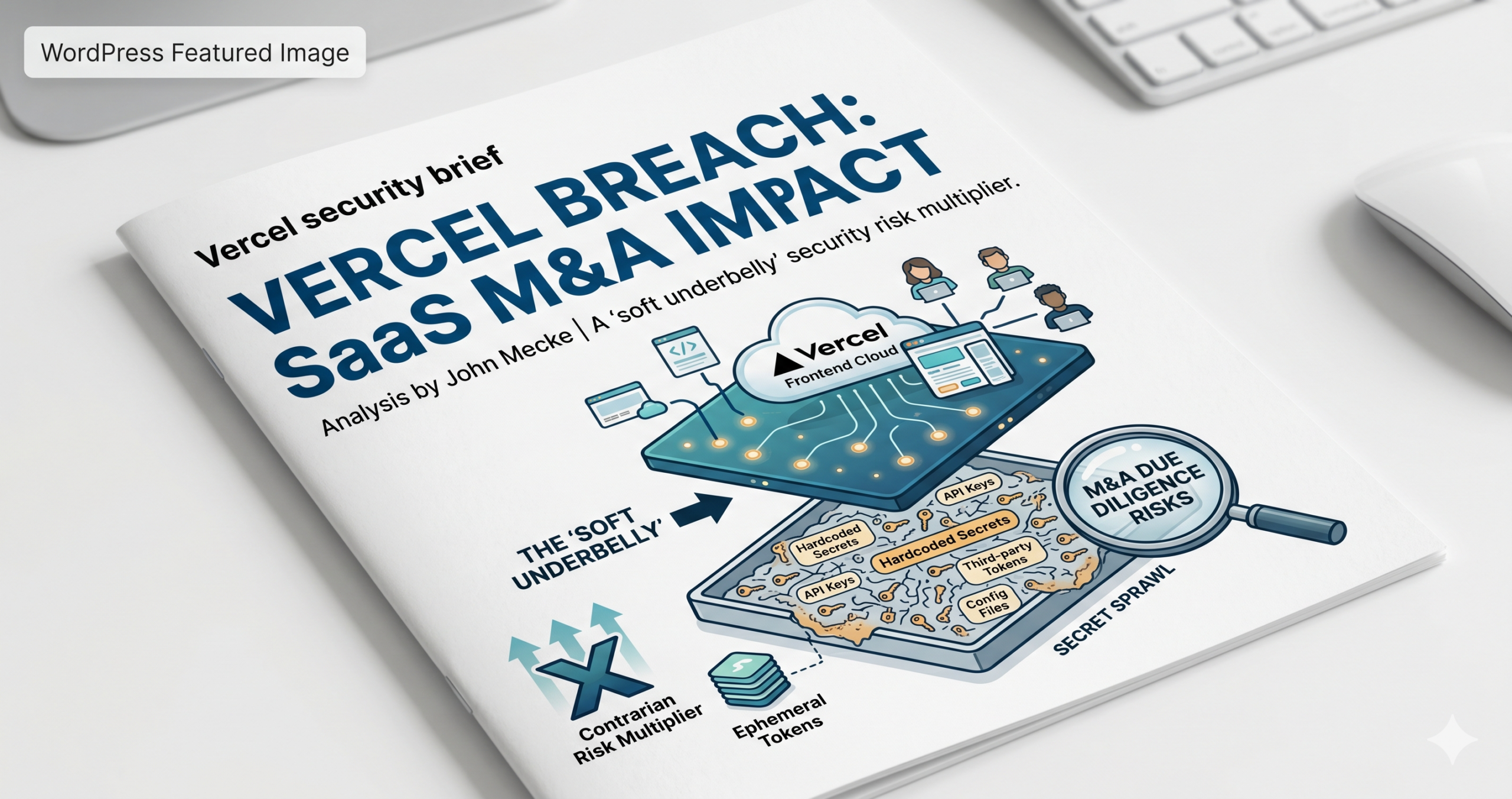
The recent confirmation by Vercel of a security breach—following claims by hackers (purportedly linked to ShinyHunters) selling internal access, source code, and API keys—is not just another entry in the 2026 data breach log. For the Private Equity (PE) firms currently roll-up shopping in the DevTools space and the SaaS founders building on “modern” stacks, this is a structural warning.
The market has spent five years fetishizing the “Frontend Cloud.” We’ve treated abstraction layers like Vercel as friction-reducers. But in our rush to achieve deployment velocity, we have ignored the compounding Supply Chain Technical Debt being accrued.
The Contrarian Thesis: Abstraction is a Risk Multiplier, Not a Security Layer
The consensus view of Vercel and its peers (Netlify, Cloudflare Pages) is that they “solve” security by removing the need for developers to manage servers. The reality? They concentrate risk into a single, high-leverage point of failure.
When you move your environment variables, NPM tokens, and GitHub hooks into a third-party CI/CD orchestrator, you aren’t eliminating risk; you are outsourcing the “Keys to the Kingdom” to a vendor whose primary incentive is developer experience, not hardened defense. For an acquirer, a target company’s reliance on these platforms is no longer a “modernity signal”—it is a due diligence red flag that requires a deep-dive into Secret Sprawl.
1. The Gap Thesis: The Distance Between “Serverless” and “Secure”
Vercel’s disclosure mentions a “limited subset of customers” and advises reviewing environment variables. The gap here is the distance between Platform Compliance and Operational Reality.
- The Vendor Claim: “We provide a secure, SOC2-compliant deployment pipeline.”
- The Empirical Reality: If an attacker gains access to internal Vercel systems (as claimed via Linear and internal dashboards), the “Blast Radius” extends to every GitHub repo connected to that platform.
In the SaaS M&A world, we often see “Cleanroom” audits of the codebase, but we rarely see audits of the Deployment Pipeline Permissions. If the hacker’s claims of possessing NPM and GitHub tokens are true, they didn’t just steal data; they stole the ability to inject malicious code into the next production build of every Vercel customer.
<img src=”image_4.png” alt=”SaaS Supply Chain Blast Radius Diagram” width=”100%” />
2. Audience Insights & Callouts
🟢 For Private Equity & VC Investors
The Diligence Pivot: Stop asking if the target is “on the cloud.” Start asking for a Service Identity Audit. In the “Free Money Era” (2020-2021), we ignored these dependencies. In 2026, a breach of a core infrastructure provider can devalue a portfolio company by 30% overnight due to customer churn and reputational damage. If your target uses Vercel, your technical due diligence must now include a “Secret Rotation Protocol” check.
[Internal Link: The SaaS Exit Crisis: A Survival Guide for CEOs Navigating the AI Era in 2025]
🟡 For SaaS Founders
Velocity vs. Vulnerability: You likely chose Vercel to hit $10M ARR faster. But if you are preparing for an exit, “Secret Sprawl” is your silent valuation killer. Buyers in this high-interest-rate environment are looking for reasons to “re-price” your deal. Don’t let a breach at your provider be their leverage. Implement Sensitive Environment Variables and hardware-based MFA for all deployment triggers today.
[Internal Link: Why 22% of SaaS Deals Are Lost in the Needs Assessment Stage]
🔵 For CTOs & CPOs
The Architectural Debt: You’ve traded architectural control for deployment speed. This breach proves that the “Front-end Cloud” is a massive, unmanaged supply chain risk. It’s time to evaluate Egress Filtering for your serverless functions and moving toward OIDC-based authentication for your CI/CD pipelines to eliminate long-lived tokens.
3. The $2 Million Extortion: A Pricing of the “Developer Trust”
The reported $2 million ransom demand is peanuts compared to the enterprise value at stake. Vercel is the backbone of the Next.js ecosystem. If the “ShinyHunters” group—or whoever is behind this—actually possesses the source code for Vercel’s internal routing or edge middleware, they have the blueprint for bypassing the security of millions of web applications.For M&A professionals, this highlights a new category of Intangible Liability: Infrastructure Contamination. If a target company’s secrets were exposed in this breach, their entire historical codebase might be “poisoned” in the eyes of a conservative strategic buyer like Microsoft or Oracle.