When “Compliant” Means Nothing: The Delve Scandal and the Fake Compliance SaaS Due Diligence Crisis No One Is Talking About
Fake compliance in SaaS due diligence is no longer a theoretical risk. It is a documented operational reality — and it may already be sitting inside your portfolio company’s vendor stack, your acquisition target’s compliance documentation, or the third-party security attestations your enterprise procurement team accepted at face value.
That is the conclusion every M&A buyer, PE investor, and enterprise CTO should draw from the Delve scandal that broke this week. On March 21, 2026, TechCrunch reported that Delve — a Y Combinator-backed GRC compliance startup that raised a $32 million Series A at a $300 million valuation from Insight Partners — stands accused of systematically generating fabricated audit reports for hundreds of clients, using rubber-stamp auditors, and telling those clients they had achieved 100% compliance when they had not.
The scale is significant. The implications are worse.
| The contrarian read: This is not a story about one fraudulent startup. It is a stress test that has just failed for the entire category of AI-native compliance SaaS — and it reveals a structural blind spot in how SaaS M&A due diligence treats compliance documentation. |
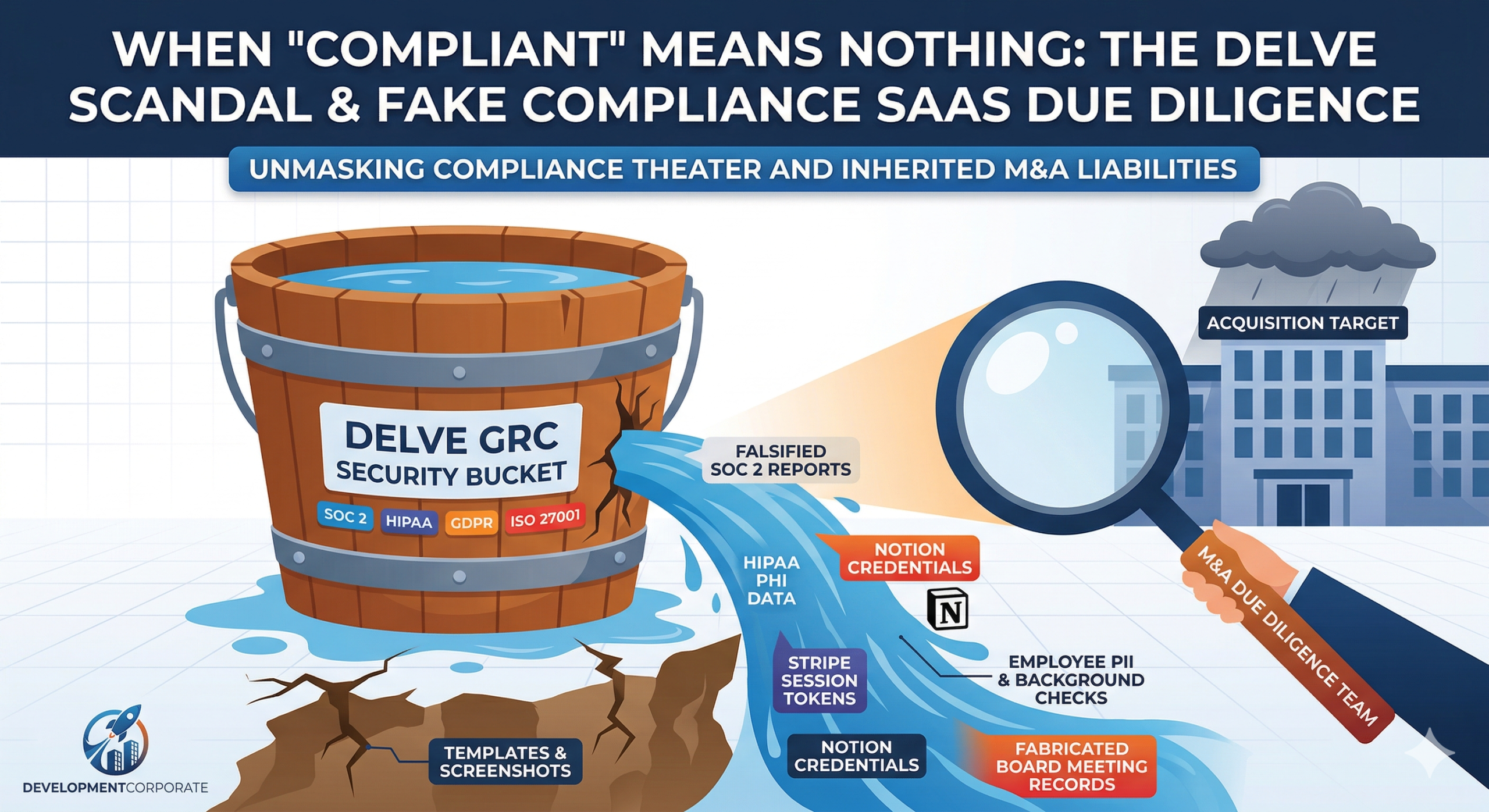
The Delve Story: Compliance as Theater
To understand the M&A implications, you first need to understand what Delve was selling — and what it was actually delivering.
Delve was founded in 2023 by Karun Kaushik and Selin Kocalar, two Forbes 30 Under 30 MIT dropouts who positioned the company as an “AI-native” platform for SOC 2, HIPAA, ISO 27001, and GDPR compliance. The pitch was speed: get compliant in days, not months, using proprietary agentic AI that automatically collected evidence, wrote reports, and monitored compliance gaps.
The reality, according to a detailed investigative Substack post published by “DeepDelver” — described as a former Delve client who pooled resources with other clients to investigate — was substantially different:
- The platform consisted primarily of pre-populated templates, manual screenshot uploads, and click-to-accept form workflows — not AI automation.
- Audit reports were generated by Delve itself using a scripted template, then forwarded to partnered audit firms (Accorp, Gradient, and others operating primarily from India through nominal US presences) for rubber-stamp approval.
- Auditor conclusions were written into reports before clients provided any information — a direct violation of AICPA independence requirements under AT-C Section 205.
- Trust pages displayed security certifications for measures companies had never implemented.
- When clients failed to onboard employees in time, Delve fabricated compliance evidence for those employees rather than flagging the gap.
The investigation found that identical boilerplate text appeared in 99.8% of 494 analyzed SOC 2 reports — including grammatical errors and nonsensical sentences copy-pasted verbatim across all client documents. Not two audit reports were the same, as Delve claimed — they were virtually all the same.
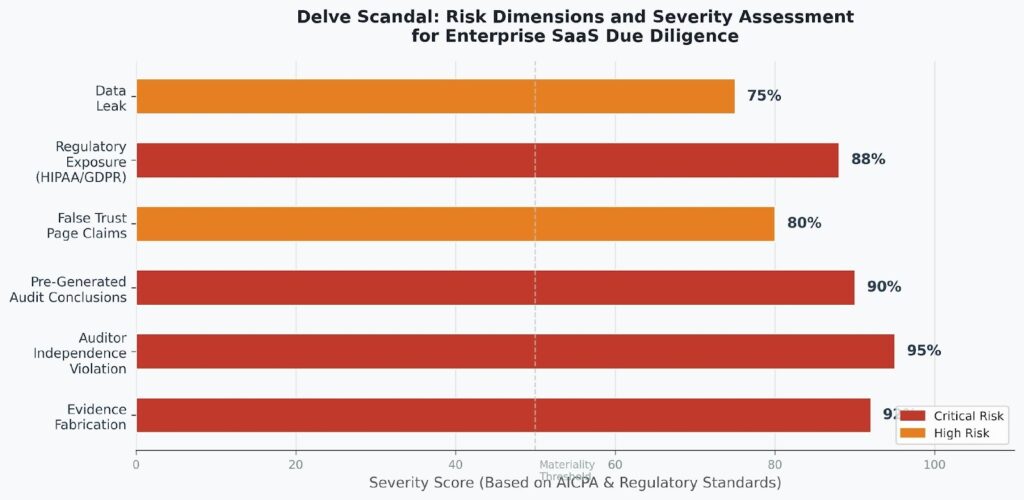
Figure 1: Risk severity assessment across six dimensions of the Delve compliance fraud allegation. Sources: AICPA AT-C Section 205, DeepDelver Substack, TechCrunch (March 2026).
In its response, Delve denied generating reports, characterizing itself as an “automation platform” that provides templates to auditors rather than producing attestations. The company described the partner audit firms as “independent, accredited third-party audit firms.” The response did not address the statistical evidence of near-identical boilerplate across all client reports.
The $300 Million Valuation That the AI Narrative Built
Delve’s $300 million valuation at Series A — approximately 9x estimated ARR based on its pricing structure — was a product of a specific market dynamic that we have analyzed in depth at DevelopmentCorporate: the AI-native premium that inflates multiples when a startup can credibly claim agentic AI capabilities.
As we explored in our analysis AI SaaS Investment Trends Are Flashing Red, the current market rewards AI-native positioning with multiples that range from 25x to 30x EV/Revenue at the Series A tier — compared to 3x to 6x for traditional SaaS platforms. Delve captured a version of that premium by claiming speed through AI when the underlying product was templated forms.
This pattern is not new. In our piece The Truth About AI Startups, we documented that 73% of venture-funded AI startups are primarily user interfaces on top of commodity APIs. The Delve case takes that pattern one step further: the “AI” was templates, and the “automation” was manual screenshots. What the AI-native narrative funded was a compliance theater operation at scale.
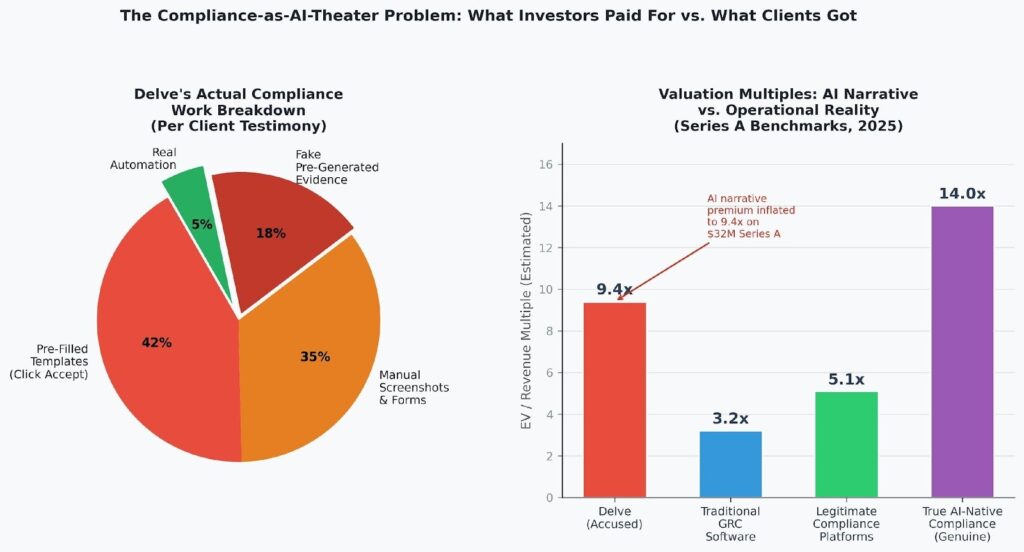
Figure 2: Left — breakdown of actual client work in the Delve process per client testimony. Right — estimated EV/Revenue multiples across the GRC compliance SaaS landscape, illustrating how AI-native narrative drives valuation disconnection from operational reality.
| The Insight Partners-led Series A at $300M implies investor belief in genuine AI-driven scalability. The Delve investigation suggests investors funded a compliance template business with an AI story — a dynamic we warned about in our analysis of the AI bubble’s structural vulnerabilities. |
Why This Is an M&A Due Diligence Crisis, Not Just a Startup Scandal
The Delve story matters to M&A practitioners for a reason that goes beyond reputational damage to one startup: SOC 2 compliance certifications are a front-line due diligence artifact.
In virtually every enterprise SaaS acquisition, the buyer’s due diligence team treats a clean SOC 2 Type II report as a meaningful signal of operational security maturity. It reduces technical due diligence time. It provides contractual protection. It informs risk adjustments to valuation models. It is cited in representations and warranties.
If those reports are generated by a platform that fabricated evidence, pre-wrote auditor conclusions, and partnered with rubber-stamp certification mills, then the entire compliance documentation layer of an acquisition target may be worthless — or worse, may represent undisclosed regulatory liability that transfers to the acquirer at close.
Our M&A Due Diligence Checklist identifies legal and regulatory compliance review as one of eight essential due diligence areas. What the Delve case reveals is that compliance review must now include a meta-layer: verification that the compliance certifications themselves were legitimately produced.
The Three Inherited Liabilities Acquirers Must Price
- HIPAA criminal exposure: Companies that processed protected health information while relying on fraudulent compliance attestations may face criminal liability. HIPAA’s willful neglect provisions include prison time. An acquirer who inherits a target with undisclosed HIPAA exposure after relying on a Delve-generated attestation has a serious problem.
- GDPR fines up to 4% of global annual revenue: For any acquisition target serving EU data subjects, GDPR non-compliance is a quantifiable liability that dwarfs most SaaS deal representations and warranties insurance coverage.
- Trust page misrepresentation: If the target’s vendor trust page — used to close enterprise deals — listed security controls that were never implemented, every enterprise customer contract entered under those representations carries potential breach exposure.
The GRC Compliance SaaS Due Diligence Checklist You Need Now
The Delve scandal requires a new verification layer in any M&A process where the target company holds AI-assisted compliance certifications. The following checklist applies across SOC 2, ISO 27001, HIPAA, and GDPR attestations.
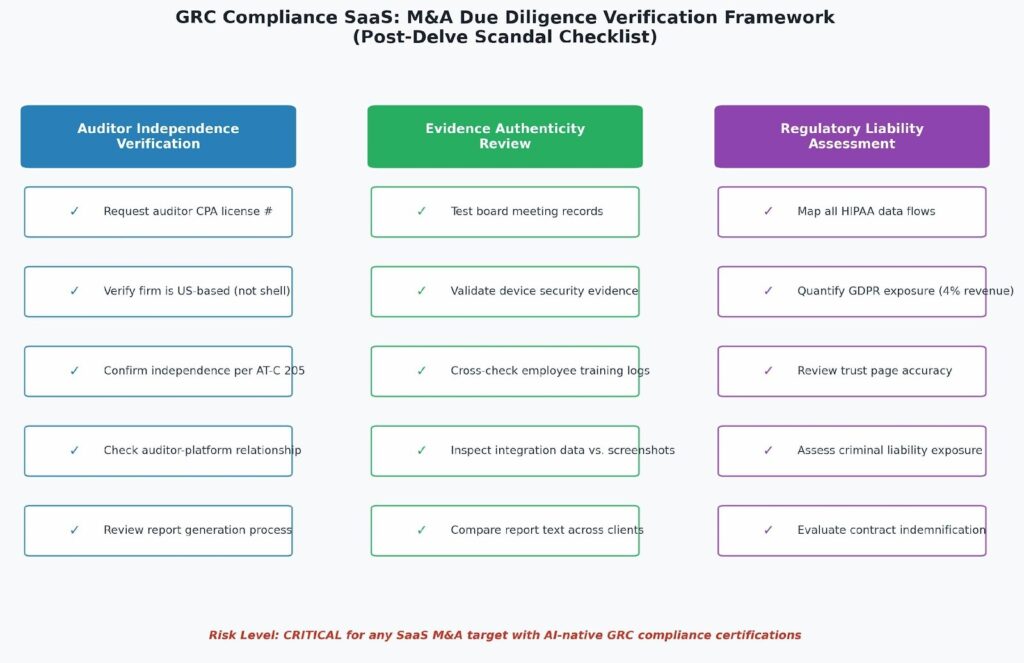
Figure 3: M&A due diligence framework for GRC compliance SaaS verification — three-pillar assessment for any acquisition target holding AI-assisted compliance certifications.
Auditor Independence Verification
- Request the auditor’s CPA license number and verify directly with the relevant state board. “US-based” firms operating through mailbox agents are not independent US CPA firms under AICPA standards.
- Confirm the auditor-platform relationship. A legitimate engagement has the auditor independently accessing evidence. Red flag: the platform generates the final report and the auditor signs it.
- Obtain the audit engagement letter. It should pre-date the compliance process, not be generated at the end. If the platform provided the engagement letter template, independence is compromised.
- Cross-check audit firm activity with public databases. Indian certification mills operating through shell US presences (like the Accorp and Gradient operations described in the DeepDelver investigation) will have minimal professional presence, no peer reviews, and no engagement history outside platform-referred clients.
Evidence Authenticity Review
- Request raw evidence samples: actual board meeting minutes (with dates, attendees, resolutions), device security configuration exports (not screenshots), and employee training completion logs from the LMS platform — not from the compliance platform.
- Compare the target’s SOC 2 report text against published Delve client reports (now publicly archived). Identical boilerplate — particularly the phrases “An Endpoint Security Solution is installed with the feature of scanning the device automatically” or “The infrastructure comprises cloud architecture including database, networking devices, virtual servers, etc.” — are markers of the Delve template.
- Ask for evidence of penetration testing from an independent firm, not a vulnerability scan from a SaaS tool that the compliance platform counts as equivalent.
- Validate that the trust page accurately reflects implemented controls — not aspirational defaults from a GRC platform template.
Regulatory Liability Assessment
- For any target processing PHI, map actual HIPAA technical safeguard implementation — not the policy documentation that says it is implemented. Disk encryption, access controls, and audit logs must be verifiable in the infrastructure configuration.
- Quantify GDPR exposure: identify all EU data subject records, confirm the legal basis for processing, and verify consent and deletion procedures are operational rather than documented.
- Review contract representations: if the target’s enterprise contracts relied on trust page certifications or SOC 2 reports that are now under question, those contracts may contain cure-or-terminate provisions that create revenue risk post-close.
What Enterprise Buyers and Portfolio Companies Must Do Immediately
The Delve situation creates a time-sensitive action requirement for three distinct groups.
For M&A Buyers Currently in Diligence
If your acquisition target holds a SOC 2 or ISO 27001 certification from the past 24 months, add GRC platform audit to your diligence workstream immediately. Ask: what compliance automation platform did you use? If the answer is Delve, the entire compliance documentation stack must be treated as unverified until independently assessed.
This is not about penalizing the target for choosing a vendor that may have misled them. It is about accurately pricing regulatory liability before close. Our analysis of enterprise SaaS M&A Q3 2025 data shows that valuation multiples in cybersecurity and compliance software commanded a 2x to 4x premium over other SaaS subsegments. That premium was predicated on the assumption that compliance infrastructure is genuine. If it is not, you are paying a premium for a liability.
For PE Investors with Portfolio Companies
Conduct an immediate portfolio audit of GRC platform usage. Any portfolio company that used Delve should: (1) unpublish its trust page pending re-verification, (2) engage an independent Big 4-adjacent CPA firm for a compliance gap assessment, and (3) notify enterprise customers proactively — before they discover the issue themselves.
The cost of proactive disclosure is substantially lower than the cost of discovery during a follow-on investment process or exit. We documented this dynamic in our analysis of the AI bubble’s structural vulnerabilities: companies built on narrative rather than operational substance face disproportionate downside when the narrative collapses. A compliance fraud exposure is not a narrative problem — it is a legal and regulatory liability that must be addressed operationally.
For Enterprise CTOs and CISOs
Your vendor compliance certifications are a trust signal you pass to your own enterprise customers. If one of your SaaS vendors used Delve to produce its SOC 2 or HIPAA attestation, and that attestation is invalid, you may have onboarded a vendor with material security gaps you did not detect — and made representations to your own customers based on those certifications.
Update your vendor security assessment questionnaire to include: “What compliance automation platform did you use to prepare your SOC 2 report?” and “Who is the independent CPA firm that conducted your audit, and can you provide their AICPA peer review number?” These are not invasive questions. They are basic verification that any legitimate compliance engagement should answer immediately.
The Broader AI-Native Compliance Problem
The Delve scandal is the most documented example of compliance theater in the AI-native GRC category, but it is unlikely to be the only one. The structural incentives that allowed Delve to scale this approach are present across the compliance automation market.
GRC automation platforms are rewarded by the market for speed. The faster they can get a company to a certified state, the better their NPS, the stronger their case study library, and the more compelling their Series A narrative. Real compliance is slow because it requires genuine evidence collection, independent testing, and actual remediation of gaps. These things cannot be templated.
The pattern mirrors what we documented in our analysis of AI-washing across the SaaS landscape: when the market rewards AI claims over operational substance, founders are incentivized to optimize for the story rather than the product. In compliance SaaS, that incentive misalignment has regulatory consequences that extend far beyond the startup itself to every company that trusted its attestations.
| The key question for every AI-native compliance platform: Does the speed claim come from genuine automation — or from skipping the steps that make compliance meaningful? The Delve investigation suggests the latter. The market has not yet priced this risk across the category. |
For M&A buyers evaluating compliance SaaS targets in 2026, the Delve case creates a new category of diligence risk: compliance platform provenance. The question is no longer just “is this company compliant?” It is “who said so, how did they verify it, and do those verifications hold up to independent scrutiny?”
As we argued in our Agentforce Illusion analysis, the due diligence question for AI-native software is never “has this company integrated AI?” It is “does the AI implementation do what it claims?” For compliance SaaS specifically, that question just acquired a new dimension: does the platform produce genuine compliance, or the appearance of it?
Update: Delve’s Own Security Failed the Same Test It Was Selling
Since this article was drafted, a second independent disclosure has compounded the original allegations — and it removes whatever remained of the “disputed claims” framing.
On March 20, 2026, security researcher James Zhou (@jameszhou02) published a thread on X that garnered 854,000 views. Zhou disclosed that Delve’s own Supabase storage bucket was publicly accessible via any signed URL token — meaning any client who had ever received a download link from Delve could access the entire bucket without additional authentication.
The exposed data included:
- Employee background checks — identity documents, address history, criminal records for Delve’s own employees and, potentially, client employees whose data was stored on the platform
- Equity vesting schedules and grant amounts — confidential cap table data
- Performance reviews — internal HR records
- Session tokens for Stripe, Notion, and other integrated services — live authentication credentials that enabled active account takeover during the exposure window
Zhou also disclosed that he obtained access to Delve’s Notion workspace.
| The session token exposure is the most legally significant element. Unlike static documents, session tokens represent live access credentials. During the window they were exposed, anyone with a signed URL could have authenticated into Delve’s Stripe billing account and Notion documentation environment — not just read files, but taken authenticated action. |
The Supabase Misconfiguration Explained
The technical failure is a well-documented Supabase storage misconfiguration. Signed URLs in Supabase are designed as time-limited access tokens for private bucket objects. However, when bucket-level Row Level Security policies are misconfigured — or when the same signed URL pattern is reusable — any recipient of a prior URL can access the full bucket scope.
Supabase’s own documentation notes that once a signed URL has been issued, it bypasses RLS policies and goes directly to the S3 bucket. Delve apparently stored highly sensitive files — background checks, equity records, session tokens — in a bucket where URL reuse enabled unrestricted access.
For a company whose core product is certifying other companies’ security controls, this is not a minor operational error. It is a direct contradiction of the security posture the platform was selling.
What This Adds to the M&A Due Diligence Framework
The Zhou disclosure changes the due diligence calculus in one specific way: it converts the Delve story from disputed allegations into confirmed security failures.
The DeepDelver Substack investigation was detailed and well-documented, but Delve disputed it. The Zhou disclosure is technically verifiable — Supabase storage misconfigurations are reproducible, the exposed data types were documented with screenshots, and the session token exposure is not a matter of interpretation.
For acquirers evaluating any target that used Delve: the platform that certified your target’s security controls had live session tokens for its own billing and documentation systems sitting in a publicly accessible storage bucket. The question is not whether to re-verify the target’s compliance certifications. The question is whether those certifications should be treated as having any evidentiary value at all.
The three-layer structure of this story now reads:
- Layer 1 — Delve allegedly faked client compliance certifications across 494 reports, using rubber-stamp auditors and pre-generated evidence (DeepDelver Substack)
- Layer 2 — Delve denied the allegations and called the evidence misleading (Delve blog response)
- Layer 3 — Delve’s own Supabase bucket was publicly accessible, exposing employee PII, equity data, and live session tokens (James Zhou, @jameszhou02, 854K views)
A company that cannot secure its own storage bucket is not a compliance vendor. It is a liability factory — and at $32 million in committed capital, it is a liability factory with a $300 million narrative attached to it.
The Bottom Line
The Delve scandal is a case study in what happens when the AI-native valuation premium meets a category where the product’s core function is trust — and the delivery mechanism is theater. The James Zhou disclosure adds an exclamation point: the compliance vendor certifying your vendors’ security had live session tokens in a publicly accessible storage bucket.
Hundreds of companies may currently be operating under compliance certifications that are legally invalid. Their enterprise customers may be relying on security claims that were never verified. Their investors may hold portfolio positions where the compliance infrastructure that enterprise deals were closed on does not exist. And the vendor’s own security posture has now been independently confirmed to have failed a basic configuration check.
For M&A practitioners, this means adding a new mandatory layer to every deal involving a SaaS target that holds AI-generated compliance certifications: independent verification of the compliance certification process itself, not just the certificate — and independent security review of the compliance platform vendor’s own infrastructure posture.
The cost of that verification is a few weeks of additional diligence. The cost of discovering it post-close — with HIPAA criminal exposure, GDPR liability at 4% of global revenue, customer contracts built on security claims that were never implemented, and a vendor whose own Stripe and Notion credentials were sitting in an open bucket — is substantially higher.
| Is your portfolio or acquisition target using an AI-native compliance platform?DevelopmentCorporate provides compliance provenance audits as part of enterprise SaaS M&A due diligence engagements.Contact us at DevelopmentCorporate.com |