The Delve Whistleblower Files: From Fake Compliance to Investor Fraud Allegations
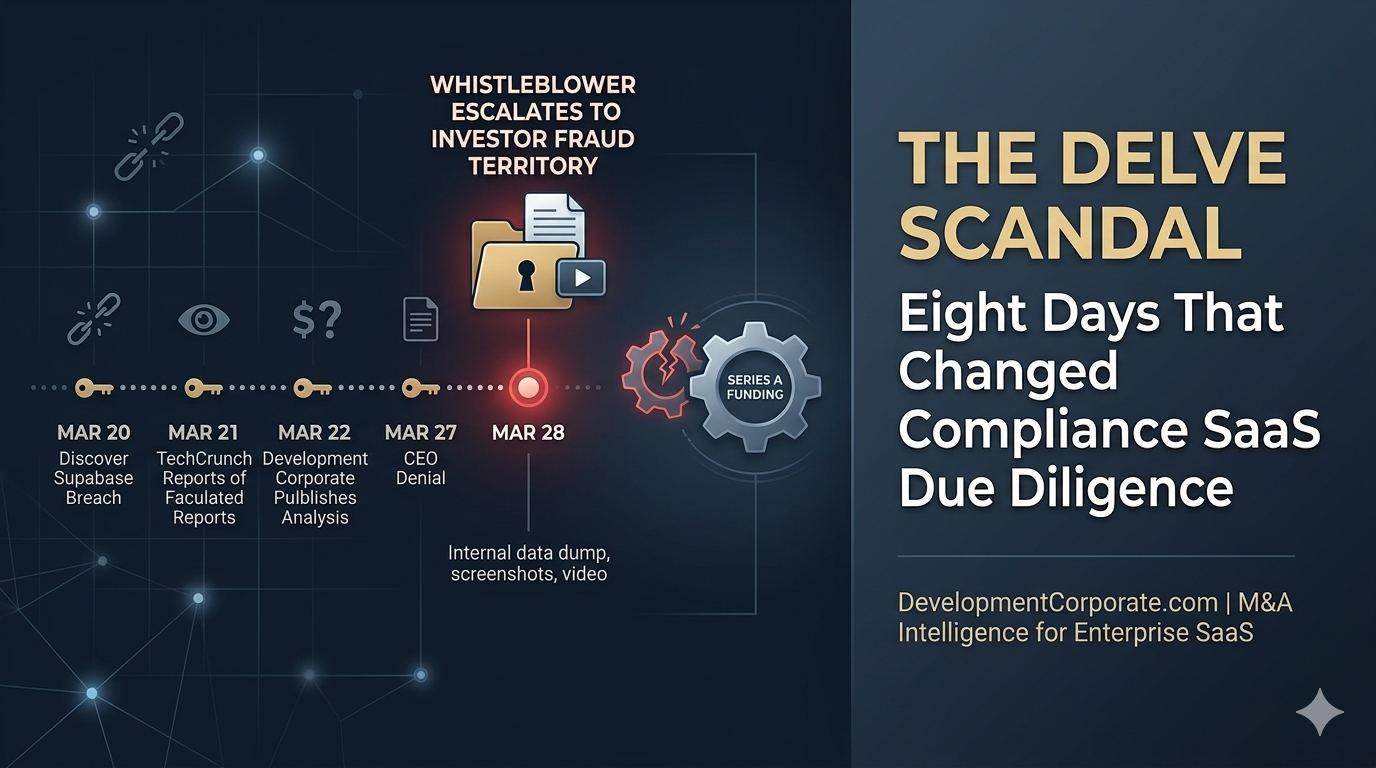
Fake compliance SaaS due diligence just entered a new phase. When DevelopmentCorporate first covered the Delve scandal on March 22, the story was alarming — but technically contested. Delve denied fabricating audit reports. CEO Karun Kaushik called the allegations misleading. The company’s investors and Y Combinator backers stayed quiet.
That framing collapsed on March 28, 2026. A whistleblower — a Delve employee — came forward and delivered to investigative Substack DeepDelver a substantial dump of internal screenshots, videos, and recorded conversations. What those materials contain is no longer a matter of disputed interpretation.
The story has crossed a threshold. This is no longer a compliance theater scandal. It is a potential investor fraud case, with Delve’s own CEO on record acknowledging in internal documents that the platform could not deliver what the Series A pitch deck claimed — during the period in which that funding was being raised.
| The contrarian read: Every M&A buyer, PE investor, and enterprise CTO who accepted Delve-generated compliance certifications at face value now has a second-order problem. The first order was fake compliance. The second order is that the company running the fake compliance platform may have also defrauded its Series A investors — and that exposure does not stay contained to Delve. |
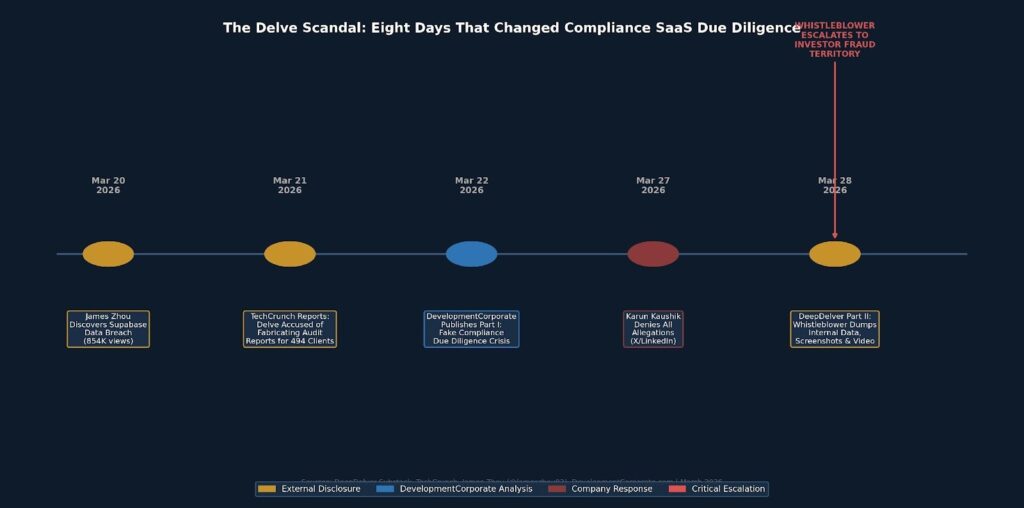
Figure 1: Eight-day escalation timeline of the Delve scandal, from the Supabase breach disclosure through the whistleblower dump. Sources: DeepDelver Substack, TechCrunch, James Zhou (@jameszhou02), DevelopmentCorporate.com.
What the Whistleblower Delivered
The whistleblower reached out after the original DeepDelver investigation published. According to the March 28 Part II post, they provided “a huge amount of data, screenshots and videos” covering internal operations, employee communications, and recorded executive conversations.
DeepDelver has committed to releasing findings daily over five days rather than holding the material for a single long-form article. Day 1 alone contained four categories of evidence that individually are significant — and collectively transform the legal character of the allegations.
Karun Kaushik responded to the original investigation on March 27 with an X/Twitter statement viewed 489,000 times, denying the core allegations. Y Combinator publicly supported the LinkedIn version of that statement. Within 24 hours, the whistleblower data had arrived.
The Accorp Exchange: Evidence That the CEO Knew
The most legally significant content in the Day 1 whistleblower release is a recorded conversation between CEO Karun Kaushik and an employee named Ross. In it, Karun asks directly:
| “Does Accorp actually look at our platform at all?” [smiles]— Karun Kaushik, CEO of Delve |
Ross responds with a laugh. The exchange then turns to liability:
| “By the way, they take all the liability. So it’s not like I’m complaining. It’s more like a risk mitigation.”— Karun Kaushik |
This exchange is not ambiguous. It shows the CEO of a compliance platform explicitly questioning whether its audit partner reviewed any evidence — and then expressing comfort with that arrangement because the liability would attach to the auditor, not Delve.
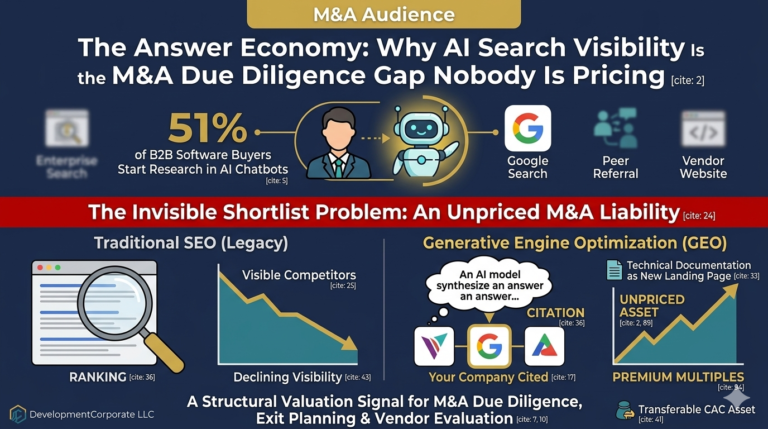
This is the core of how compliance theater scales. As we documented in our analysis of AI-washing across the SaaS landscape, the market rewards AI claims over operational substance. Here, the incentive misalignment went one step further: the compliance vendor designed its auditor relationship specifically to push liability downstream while maintaining the appearance of independent verification.
Accorp has since publicly denied any affiliation with Delve. That denial raises its own question: if the relationship was as described in the recording, who is telling the truth?
Project Audit Automation: Contradicting the Core Defense
Delve’s official response to the original DeepDelver investigation characterized the company as an “automation platform” that provides templates to auditors — not an entity that generates reports. The whistleblower data directly contradicts this.
Internal screenshots show a channel called “Project Audit Automation” with active participation from Ross Corey, Yuri Genyk, Agnes Shan, and Jayu Patel. A separate screenshot shows an internal tool described as “Selin’s Report Generator” — named after co-founder Selin Kocalar.
A separate internal message notes that “v0 of Delve AI was live” as of August 9, 2025. The timing matters: this was described internally as being built after the Series A raise.
The legal implication is direct. Delve’s public defense rested entirely on the claim that it was a template provider, not a report generator. These screenshots show an internal project named specifically for automating audit report generation — with cross-functional employee participation and a named tool for doing so.
| The question for Insight Partners and Y Combinator is now the same question their lawyers are asking: what did the company know, when did they know it, and what did they represent in the Series A materials? |
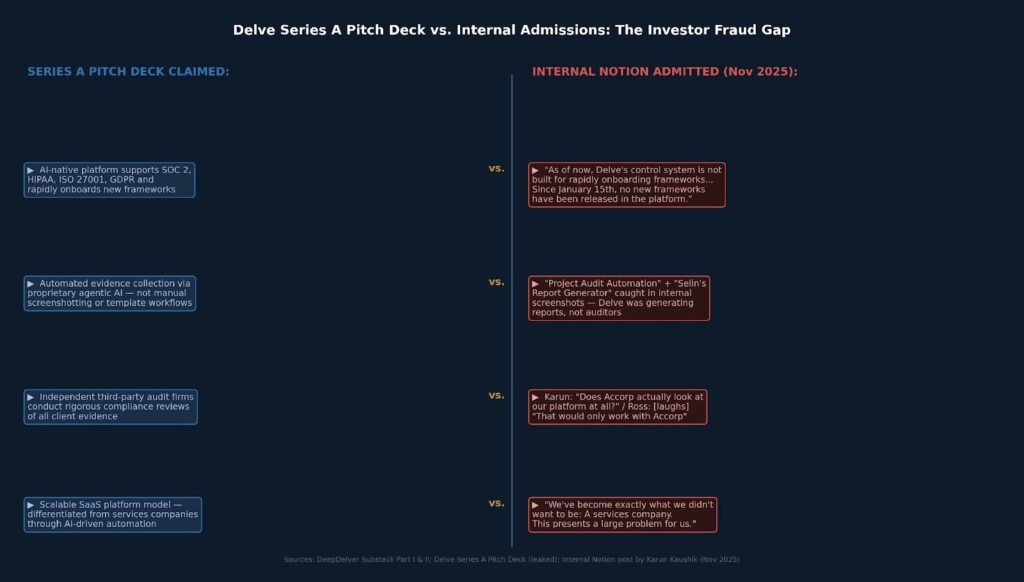
Figure 2: Direct comparison of Delve’s Series A pitch deck claims against internal Notion admissions by CEO Karun Kaushik (November 2025). Sources: DeepDelver Substack Part II, leaked pitch deck, internal Notion post.
The Pitch Deck vs. the Internal Admission: A Securities Fraud Question
The most damning element of the Day 1 whistleblower release is not the Accorp recording. It is a Notion post written by Karun Kaushik in November 2025 — during or after the Series A fundraising period — that directly contradicts the platform capabilities pitched to investors.
In that internal post, Kaushik wrote:
| “As of now, Delve’s control system is not built for rapidly onboarding frameworks in a stable manner. It was built off of the initial SOC 2 control system, and then amended and modified for HIPAA, ISO 27001, and GDPR. Since January 15th, no new frameworks have been released in the platform.”— Karun Kaushik, internal Notion post (November 2025) |
The Series A pitch deck, also released in the whistleblower data, shows Delve claiming multi-framework AI-native compliance capabilities as a core investment thesis. The Notion post was written during — or after — the period in which that capital was committed.
Kaushik continued:
| “To supplement, we’ve asked vCISOs to instead support them off-platform, and in effect become exactly what we didn’t want to be: A services company. This presents a large problem for us.” |
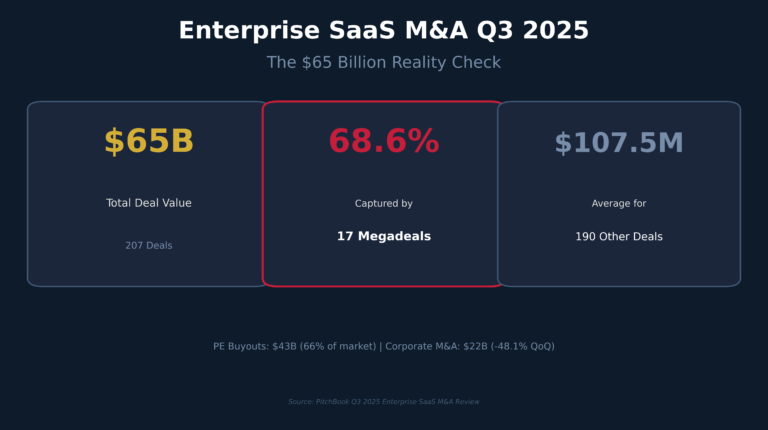
The pattern is one we’ve tracked systematically. As we documented in our AI funding bifurcation analysis, AI-native startups at the Series A tier were commanding 25–30x EV/Revenue multiples based on claims of genuine automation capability. Our AI valuation gap analysis shows that 83% of buyers paid higher multiples for AI-native positioning. Delve captured that premium by claiming capabilities that its own CEO documented internally were not implemented.
This is the point at which the Delve story crosses from compliance fraud into potential securities fraud territory. A material misrepresentation in investor materials — claiming product capabilities that internal documents show were not yet built — is the foundational element of a 10b-5 securities claim. That does not require a conviction or even an SEC filing to create serious liability exposure for the company, its founders, and potentially its lead investors.
The Auditor-Switching Gambit
Since the original allegations surfaced, Delve has communicated to clients that it is switching SOC 2 audits to a firm called Ezzy & Associates. Clients are being told they will not need to restart their SOC 2 Type 2 observation periods when switching from Accorp.
That assurance is deeply irregular. A SOC 2 Type 2 audit covers a specific observation period. Changing auditors mid-period — particularly when the original auditor has publicly disavowed any relationship with the platform — typically requires restarting the observation period with the new auditor. Telling clients they do not need to restart suggests either that Ezzy is agreeing to accept the existing evidence record, or that Delve is making a representation to clients that it cannot deliver.
Ironically, the founder of Ezzy & Associates holds a Certified Fraud Examiner (CFE) designation. Whether Ezzy is being used as a legitimate clean-slate solution or as a liability-laundering mechanism is, at this point, an open question.
Delve is also continuing its ISO 27001 work with Glocert — the same firm mentioned in the original DeepDelver investigation — despite the public attention those relationships have received.
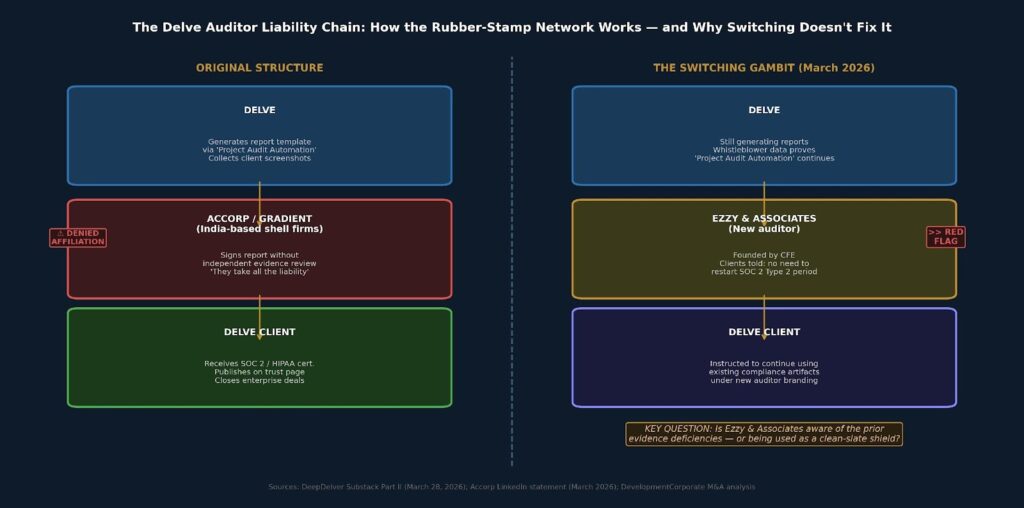
Figure 3: The Delve auditor liability chain — original structure versus the switching gambit. Key question: does Ezzy & Associates know the prior evidence is deficient, or is it being used as a compliance laundering mechanism? Sources: DeepDelver Substack Part II, Accorp LinkedIn denial, DevelopmentCorporate M&A analysis.
Y Combinator’s Position — and What It Signals
When Kaushik posted his denial on LinkedIn on March 27, Y Combinator publicly expressed support. That support now sits alongside whistleblower video of Kaushik laughing about whether his audit partner reviewed any evidence, and an internal Notion post acknowledging the platform’s core capabilities were not built.
YC’s continued backing does not make those materials disappear. What it does do is create a reputational and governance exposure for the accelerator. If the whistleblower materials prove accurate — and the Notion post is in Kaushik’s own words, in an internal system — YC’s public endorsement of a fraud denial will become a data point in any subsequent legal proceedings.
The broader market implication is one we flagged in our analysis of the AI bubble’s structural vulnerabilities: when institutional capital endorses companies built on narrative rather than operational substance, the credibility cost of that endorsement is paid when the narrative collapses. For YC, Delve is now a test case.
What This Means for M&A Due Diligence: An Updated Framework
Our original article established a three-pillar GRC compliance verification framework for any acquisition target holding AI-assisted compliance certifications. The whistleblower data requires adding a fourth pillar: executive representation risk.
The Original Three Pillars (Updated)
- Auditor independence verification — now must include inquiry into the auditor-switching history. If a target switched audit firms after the original investigation, require an explanation and a new Type 2 observation period with the current auditor.
- Evidence authenticity review — the boilerplate language flags identified in Part I remain valid. The whistleblower data adds a new marker: ask whether the compliance platform used internal tooling branded as “report generation.” If yes, the independence claim fails.
- Regulatory liability assessment — unchanged. HIPAA criminal exposure, GDPR fines at 4% of global revenue, and trust page misrepresentation remain the three quantifiable liabilities.
The Fourth Pillar: Executive Representation Risk
Any acquisition target that used Delve and is currently in a fundraising or M&A process has a new category of liability: the representations made to prior investors may now be subject to challenge.
Buyers must ask: Did the target represent to its own investors or customers that it held valid compliance certifications? If those certifications were produced by a platform whose CEO is now on record questioning whether the audit partner reviewed any evidence, those representations carry breach exposure.
This connects directly to the reps-and-warranties dynamics we analyzed in our SaaS M&A buyers’ perspective analysis. When sellers and buyers disagree about the durability of a business model, the disagreement surfaces in the multiple, the earnout structure, and the reps and warranties. Compliance fraud exposure surfaces in exactly the same place — but with criminal liability attached.
| AUDIENCE-SPECIFIC IMPLICATIONS MATRIX |
| Audience | Immediate Risk | Required Action |
| PE/VC Investors | Portfolio companies using Delve may have compliance certs that are legally invalid. New: any portfolio company that represented Delve certs to its own investors has potential rep breach exposure. | Immediate portfolio audit for Delve usage. Engage independent CPA for gap assessment. Evaluate whether representations to LPs or enterprise customers must be corrected. |
| SaaS Founders (Exit Planning) | A Delve-generated SOC 2 in your data room will be flagged in diligence. The whistleblower materials make this a binary question, not a risk-adjustment question. | If you used Delve, unpublish your trust page now and engage an independent Big 4-adjacent auditor. Proactive disclosure before LOI is dramatically cheaper than discovery during due diligence. |
| Enterprise CTOs / CISOs | Vendors you onboarded based on Delve-certified trust pages may have implemented zero of the controls listed. Your own vendor risk certifications passed to customers are now suspect. | Add two questions to your VSQ: “What compliance platform did you use?” and “Can you provide your auditor’s AICPA peer review number?” Require re-certification from any vendor that used Delve. |
The Bottom Line
Eight days ago, the Delve story was a compliance theater scandal. A startup faked audit reports. Its auditor partners rubber-stamped the results. Hundreds of companies may be operating under invalid certifications.
Today, the story is something more serious. A whistleblower has provided internal recordings of the CEO laughing about whether the audit partner reviewed any evidence. A Notion post in Kaushik’s own voice documents that the platform’s core AI capabilities — the ones pitched to Insight Partners — were not built during the fundraising period. An internal project called “Project Audit Automation” directly contradicts the company’s stated defense.
The auditor-switching play — moving to Ezzy & Associates while telling clients they do not need to restart observation periods — either represents a legitimate remediation path or a compliance liability laundering mechanism. At this point, buyers and investors cannot assume the former.
For M&A practitioners, the action item is the same as we stated in our M&A due diligence checklist update — but with greater urgency. Treat any Delve-generated compliance certification as having no evidentiary value until independently re-verified. Treat any acquisition target that used Delve and is currently in a fundraising process as carrying a potential prior-representation liability that must be scoped before LOI.
The cost of that verification is measurable. The cost of discovering it post-close — with HIPAA criminal exposure, GDPR fines, and securities misrepresentation claims layered on top — is not.
| Is your portfolio company or acquisition target using an AI-native compliance platform? DevelopmentCorporate provides compliance provenance audits as part of enterprise SaaS M&A due diligence engagements. Contact us at DevelopmentCorporate.com |